How to Train Your Team on Network Encryption Best Practices
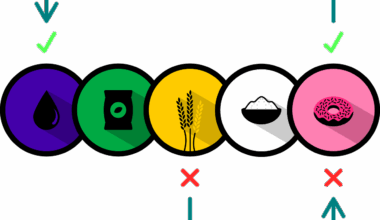
Training your team on network encryption best practices is a vital step in securing sensitive information and ensuring data integrity. A comprehensive understanding of encryption methods reduces the risk of data breaches and unauthorized access. Start by introducing the basic concepts of encryption, including symmetric and asymmetric algorithms. You can explain key terms like keys, plaintext, ciphertext, and block ciphers. Today’s teams must grasp the differences between various encryption standards such as AES, RSA, and Blowfish. Use engaging visual aids or videos to illustrate how these encryptions operate in real time. The more visual you are in your presentation, the better your team will retain the information presented. Furthermore, you could hold ongoing workshops or training seminars to reinforce these concepts and discuss recent updates in the field of encryption technologies. Make sure to integrate hands-on exercises to allow team members to apply what they have learned practically. This active approach will solidify their understanding and build confidence in utilizing these technologies effectively, ensuring that your organization remains compliant with industry standards. Regular assessments can also help gauge their comprehension and areas needing improvement.
One of the essential components of training your team is to provide them with an understanding of secure communication protocols. Focus on protocols such as SSL/TLS, IPsec, and SSH, which play a pivotal role in securing data in transit. Ensure that your team includes not only technical staff but also non-technical employees who can benefit from understanding these protocols. You can create summary documents or infographics that break down complex concepts into digestible pieces. In addition, facilitate discussions around the importance of implementing strong cryptographic policies. This includes password complexity, key management practices, and regular audits of encryption configurations. Encourage your team to stay updated on evolving threats and vulnerabilities that may affect network encryption. Resources like security blogs, newsletters, or cybersecurity forums can be beneficial for continuous learning. Furthermore, consider promoting a culture of security within your organization by encouraging open discussions about encryption challenges faced by the team. By sharing experiences and knowledge, you foster an environment where the importance of secure communication becomes common practice. Although it may take time, establishing engagement and awareness can lead to a more security-conscious workforce.
Practical Implementation of Encryption Techniques
When training your team on encryption best practices, real-world scenarios can dramatically enhance learning outcomes. Begin by simulating common situations they might encounter in their daily tasks. Practical exercises, such as encrypting files or configuring VPNs, allow team members to experience the encryption process firsthand. Implement case studies highlighting past data breaches to underline why robust encryption is essential. Analyzing these cases in group discussions provides insight into what went wrong and how encryption could have mitigated these issues. Utilize platforms that offer virtual labs for hands-on training in a controlled environment. This active participation will prepare them for real-world challenges. Use tools like Wireshark to demonstrate eavesdropping techniques, proving the necessity of encryption. Interactivity is key in effective training, so make use of quizzes or gamification to test knowledge retention. Offering incentives such as certificates or recognition can encourage enthusiasm for learning. Always gather feedback after training sessions to improve and tailor the experience. Continuous enhancements to the training program ensure it remains relevant to current threats, keeping your organization’s defenses up to date.
Regular updates and refreshers are crucial components of training your team on encryption techniques. Cyber threats continually evolve, and so must your team’s knowledge and skills. Establish a recurring schedule for ‘encryption clinics’ or quick workshops focusing on the latest developments in network encryption. These informal sessions can cover topics like current encryption technologies or recent vulnerabilities in common encryption platforms. Encourage team members to present on topics they’ve researched or explored, fostering shared learning. Additionally, recognize the importance of promoting a culture of continuous learning. Subscribe your team to trusted cybersecurity newsletters or journals that focus on network encryption. These resources can provide valuable insights and inspire discussions during team meetings. Empower your employees to create a knowledge-sharing platform within your organization, allowing them to post articles or findings about encryption. Adopting new tools for better encryption management can also be beneficial. Equip your team with resources like encryption management software, providing them with functionalities that simplify their tasks while boosting security. Educating employees about the importance of reporting any suspected vulnerabilities or incidents is essential for reinforcing responsibility across your organization.
Developing a Security-Focused Mindset
Incorporating a security-focused mindset into your team is essential for enhancing their understanding of encryption best practices. Foster discussions on the significance of cybersecurity in daily workplace activities and highlight the implications of poor encryption. Encourage employees to ask questions and share their concerns regarding network security to create a supportive environment. Promote an understanding of the regulations surrounding data protection, such as GDPR or HIPAA, to illustrate the necessity of encryption solutions. Ensure your team comprehends how encryption protects not only company data but also customer information, fostering trust. Introduce the concept of risk management, discussing the potential risks associated with weak encryption. Identify and accept that security is a continuous process that evolves with emerging technology. Regularly update your team on best practices and recommend attending workshops or conferences that focus on encryption and cybersecurity. Support their professional growth in this area. Creating opportunities for certifications in encryption and cybersecurity can also solidify their understanding. A knowledgeable and certified team demonstrates not only compliance but your organization’s commitment to protecting sensitive data, enhancing its reputation in the market.
Finally, measure and evaluate the effectiveness of your training program to ensure the team grasped encryption best practices. Develop key performance indicators (KPIs) such as knowledge assessments, incident response times, or reduced data breaches. Regularly review the success of the training modules and confer with the team regarding challenges encountered while implementing the learned techniques. Addressing these issues can provide valuable insights for future training sessions. After assessments, share the results with the team to acknowledge their achievements and areas for improvement. Offer follow-up training or resources to help those who need additional support. Conduct discussions that allow them to brainstorm solutions collaboratively, promoting a sense of ownership and responsibility towards implementing encryption best practices. Additionally, create a timeline for providing periodic refresher courses, adapting to their feedback and focusing on identified weaknesses. Engage team leaders or influential members to champion encryption advocacy within the organization. A steadfast commitment to training and keeping your team informed helps develop a proactive security culture. By valuing ongoing education and fostering a positive learning environment, you solidify your organization’s resilience against cyber threats.
Conclusion and Future Directions
In conclusion, empowering your team with knowledge on network encryption best practices is a pivotal aspect of securing sensitive data and maintaining organizational integrity. The methods discussed highlight the importance of a comprehensive and engaging training approach that includes both foundational knowledge and practical implementations. Foster a culture of learning where team members feel comfortable sharing and exploring encryption technology developments together. Make sure updates to your training material occur regularly to stay aligned with advancements in technology. Adopt a proactive approach to encryption challenges, preparing your team to handle real-world cyber threats effectively. Collaborate with them on establishing and adhering to best practices, creating an environment where security becomes everyone’s responsibility. Moving forward, stay abreast of upcoming encryption techniques and legislative changes that may affect operational needs. Continuous adaptation to these factors ensures your organization’s methodologies remain current and effective. Ultimately, a well-trained team equipped with up-to-date knowledge on encryption not only improves your security posture but fosters trust with clients and stakeholders. As threats evolve, so should your team’s preparedness to counter them effectively, securing your network and data.
By prioritizing training on network encryption best practices, your organization positions itself as a forward-thinking leader in cybersecurity. Continually emphasize the growing importance of encryption for protecting sensitive information. Ensure that your training sessions are interactive and relatable, incorporating examples relevant to your team’s daily tasks. Organizations that invest in their team’s understanding of encryption methods experience reduced risks of data breaches, instilling confidence within their workforce. Recognize that maintaining security in today’s digital landscape is an ongoing journey. As new technologies emerge, keep your training procedures dynamic and responsive. In the long run, your outreach contributes to a more knowledgeable workforce, better equipped to implement encryption strategies seamlessly. Foster relationships with cybersecurity experts and thought leaders to harness best practices and emerging trends. Encourage continuous dialogue surrounding encryption and its ties to overall organizational security. By cultivating a strong encryption foundation, your organization is not only preparing for current challenges but also anticipating future developments. Position your organization as a role model in cybersecurity adherence and resilience, leading by example, while safeguarding valuable digital assets and information with confidence.